Understanding the GDPR
First, it is important to understand why you have to observe the GDPR (General Data Protection Regulation) at all, how that helps you to implement the GDPR, and what the meaning of this data protection directive is.
The General Data Protection Regulation is a European data protection law that defines in what way and how specific categories of personal data may be processed.
It applies to all data processing operations by European persons or data processing operations conducted in Europe. The territorial principle therefore also affects companies that are not based in Europe – so even if the companies are not settled in a member state of Europe.
Example: Extra-Territorial scope

An American company processes data - personal information - from European individuals outside of Europe. The company must comply with the GDPR.
A Canadian company evaluates data from European individuals. The company must comply with the GDPR.
A company in Asia, Africa, or America performs software and cloud maintenance work for another company that stores and evaluates data from Europeans. The European company must ensure that the third party (in this example the maintenance company) operates at the level of the GDPR.
The GDPR therefore not only affects Europe but also goes beyond European borders.
Penalties and fines when breaking this data protection act
The penalties of the GDPR are intended to function as a deterrent and are therefore extremely high. They can amount to up to 20 000 000 EUR, or in the case of an undertaking, up to 4 % of the total worldwide annual turnover of the preceding financial year, whichever is higher. The amount of these fines is influenced by the type, amount, and duration of the violations as well as a variety of other aspects. But even lower penalties often range from $25,000 to $100,000.
Accountability
Since you as an entrepreneur have accountability, you should always be able to answer the following questions, for example:
Are my customers' data stored securely?
Am I even entitled to conduct the data processing that I undertake?
Do I have to designate a data protection officer and how is my data protection management system structured?
Why am I allowed to process data in the US without a valid Privacy Shield?
Do I manage my customers' consent and can I prove this?
What technical and organizational measures do I use to ensure an appropriate level of protection for the processing of the data? Do the used measures correspond to the current state of the art?
If there is a data breach and customers complain about your business to the relevant regulator - the controller -, you can expect these or comparable questions.
Controller
Is there only one controller or are there many controllers? From the point of view of the GDPR, the question of who is responsible can be solved relatively easily. The person responsible is defined in Article 4 of the General Data Protection Regulation.
Art. 4 (7) - Controller means the natural or legal person, public authority, agency, or other body which, alone or jointly with others, determines the purposes and means of the processing of personal data; where the purposes and means of such processing are determined by Union or Member State law, the controller or the specific criteria for its nomination may be provided for by Union or Member State law.
Article 4 of the GDPR contains a lot of important definitions.
You can find further information about the controller and the processor in Recital 24.
The processing of personal data of data subjects who are in the Union by a controller or processor not established in the Union should also be subject to this Regulation when it is related to the monitoring of the behavior of such data subjects in so far as their behavior takes place within the Union. To determine whether a processing activity can be considered to monitor the behavior of data subjects, it should be ascertained whether natural persons are tracked on the internet including potential subsequent use of personal data processing techniques which consist of profiling a natural person, particularly to take decisions concerning her or him or for analyzing or predicting her or his personal preferences, behaviors, and attitudes.
The subject of data processing in the US concerning European individuals is very complex because the ECJ has declared the previously applicable US Privacy Shield to be invalid. On October 7th, 2022, President Biden signed an executive order to Implement the European Union-U.S. Data Privacy Framework.
Why is that important for you? What obligations do you have to implement?
Most consulting firms and lawyers approach data protection from a problem-oriented perspective that discourages and sometimes frightens companies. However, it is not the reason the GDPR was brought to life, but rather to provide guidelines within which data processing is possible.
So, you should always decide for yourself whether you are able to pay any penalties that may affect you or implement other measures to keep your data processing secure.
In this context, please also note that it is not possible to speak generally about all categories of data. Special categories of data require a different approach to data security than personal data that is not as sensitive. If you process sensitive categories of data, then you must always have a higher standard in the areas of data protection, data security, information security, encryption, and access rights.
Basic principles of the GDPR
Article 1 of the GDPR contains the following provisions:
This Regulation lays down rules relating to the protection of natural persons about the processing of personal data and rules relating to the free movement of personal data.
This Regulation protects the fundamental rights and freedoms of natural persons and in particular their right to the protection of personal data.
The free movement of personal data within the Union shall be neither restricted nor prohibited for reasons connected with the protection of natural persons with regard to the processing of personal data.
Rules, protective rights, and the free movement of personal data
It is therefore about rules, protective rights, and the free movement of personal data. The European Commission does consent to use those data. We are thus in a state of tension in order not to commit personal data breaches. Within this state of tension, many different variants are possible.
However, it is always necessary to consider the legal regulation, the technical
implementation, and the data to be processed.
In practice, this often leads to problems, because most of the time you tend to focus on just one of the topics, instead of considering all three of them equally.
The data protection directive also provides clear guidelines for this because there is a data protection impact assessment regulation for new processes. The focus is not on banning the new process, but on ensuring that the processed data has the appropriate level of protection.
However, since a data protection impact assessment is very comprehensive and time-consuming, some companies go and ignore this requirement. This makes the process neither better nor safer in practice.
On the contrary, this behavior exposes you to the risk of penalties and fines and negative public perception in the event of data breaches.
You can find a lot of information about the DPIA in Article 35 GDPR and the following Recitals:
So, we can state at this point that it's always about:
Rules (Articles and Recitals)
Processes and their security
Personal Data
Articles and Recitals
The GDPR is a data protection law that consists of articles (i.e. the legal provisions) and recitals (explanations for a better understanding and interpretation of the article). If you look at the text of the GDPR, you will usually find a link to the relevant recital below the article. For example, Article 3 of the GDPR (territorial principle) refers to the following recitals:
By comparing the article and the recital, you get a better understanding of the application of the data protection law, and, in case of doubt, you can better weigh up whether a process is GDPR-compliant or not.
However, it is always important to observe the additional national laws of the country in which the data processing takes place and the case law of the ECJ.
You will find these primarily in the GDPR. However, there are also many regulations in individual countries that also affect the issue of data protection. The GDPR is therefore the overriding general basis and the other protective directives must also be observed to be GDPR compliant.
With a view to Europe, other European legal requirements that influence the processing of data must also be observed, such as the European Whistleblowing Directive, Standard Contractual Clauses, the new Transatlantic Data Privacy Framework, and many more.
But how exactly do we handle personal data?
To understand the GDPR, it makes sense to first deal with the principles of data processing. You can find these principles in Article 5 of the GDPR.
They are structured as follows and are also referred to as the 7 core principles of the GDPR.
7 Principles of GDPR
Lawfulness, Fairness, and Transparency
Purpose limitation
Data minimization
Accuracy
Storage limitation
Integrity and Confidentiality
Accountability
These principles describe how personal data must be processed to be GDPR compliant.
But be aware that complying with the principles does not mean that you are allowed to process data at all.
There are many other aspects that you must consider in order to be GDPR compliant. This includes encryption, security measures, binding corporate rules, the right to be forgotten, technical and organizational measures, authentication, additional privacy laws, and a lot more.
In recital 39 you will find further information on the principles of data processing.
Any processing of personal data should be lawful and fair. It should be transparent to natural persons that personal data concerning them are collected, used, consulted, or otherwise processed and to what extent the personal data are or will be processed. The principle of transparency requires that any information and communication relating to the processing of those personal data be easily accessible and easy to understand, and that clear and plain language be used. That principle concerns, in particular, information to the data subjects on the identity of the controller and the purposes of the processing and further information to ensure fair and transparent processing in respect of the natural persons concerned and their right to obtain confirmation and communication of personal data concerning them which are being processed. Natural persons should be made aware of risks, rules, safeguards, and rights regarding the processing of personal data and how to exercise their rights in relation to such processing. In particular, the specific purposes for which personal data are processed should be explicit and legitimate and determined at the time of the collection of the personal data. The personal data should be adequate, relevant, and limited to what is necessary for the purposes for which they are processed. This requires, in particular, ensuring that the period for which the personal data are stored is limited to a strict minimum. Personal data should be processed only if the purpose of the processing could not reasonably be fulfilled by other means. To ensure that the personal data are not kept longer than necessary, time limits should be established by the controller for erasure or a periodic review. Every reasonable step should be taken to ensure that inaccurate personal data are rectified or deleted. Personal data should be processed in a manner that ensures appropriate security and confidentiality of the personal data, including preventing unauthorized access to or use of personal data and the equipment used for the processing.
The question of the lawfulness of data processing always arises from Article 6 of the GDPR. Article 6 of the GDPR is a central regulation for day-to-day work. I have found very often that Article 6 is ignored in day-to-day business and data is processed without any legal basis which should be objected to generally!
One of the central questions of the GDPR is therefore:
Why are you even entitled to process personal data at all?
Data processing without any legal basis can lead to massive violations and exceedingly high fines.
You also must break down the process into its parts and always look at the process from the perspective of the person concerned. The GDPR is primarily a protection right for data subjects. This changes the perspective. The primary concern is always whether the subject’s data is secure, and if the data is processed in the form that the individual has consented to.
Example:
A person has an insurance contract with a company. The contract describes how all the data will be handled, but it does not describe exactly how incoming e-mails will be handled. The insured person sends an email to a personal email address of the insurance company - for example to j.smith@insurance.net.
At this point, the person concerned can assume that J. Smith will receive the e-mail and that the data contained in the e-mail will also be processed by J. Smith.
If the insurance company now converts its processes to team-related mailboxes and automatically forwards the incoming e-mail to a team mailbox, it violates the GDPR, because it has no legal basis for forwarding the e-mail to a team mailbox. In principle, you could map this on a contractual basis, but seriously, which company has all processes confirmed by the contractual partner? Practice and theory do not fit on top of each other at these points.
Incidentally, the example given was in Norway and the company was fined 25,000 EUR.
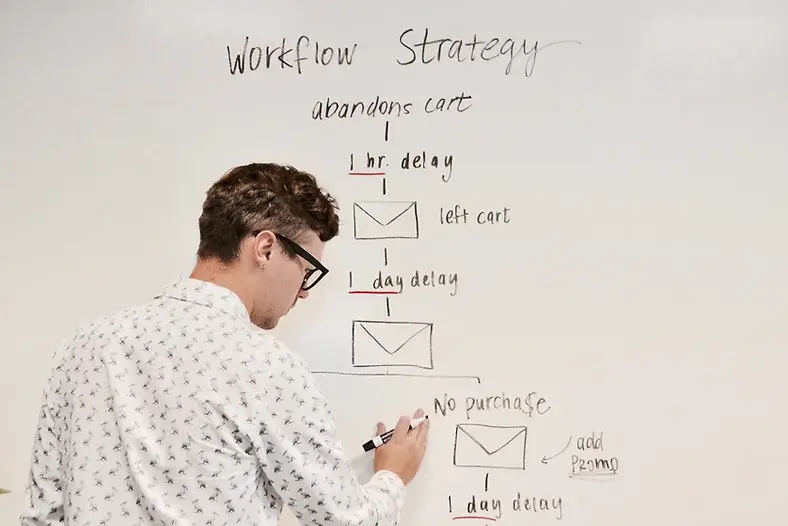
So back to the process; just because part of the process is based on a legal basis does not automatically mean that the entire process is GDPR compliant. Incidentally, the GDPR itself does not speak of processes, but of processing activities. While processing activities help design the record of processing activities, they do not help check whether a process is GDPR compliant or not.
Lawfulness of processing
The lawfulness of processing is divided into the following six sub-points:
Consent
Performance of a contract
Compliance with a legal obligation to which the controller is subject
Vital Interests of the data subject or another natural person
Performance of a task conducted in the public interest or in the exercise of official authority
Processing is necessary for the legitimate interests pursued by the controller or by a third party
Nevertheless, let’s take a look again at all the sub-points of the lawfulness of processing:
Consent - Recitals 42 and 43 / Guidelines on Consent under Regulation 2016/679
If the data processing is based on consent, the following points must be observed and implemented in practice:
Freely given, in an informed manner, for a specific purpose, all reasons for processing must be clearly stated, it must be explicit and given via a positive action like a clickable box or a signature on a form, it must use clear and plain language, and must be visible. Furthermore, consent can be withdrawn at any time.
Freely given consent means the individual must have a free choice and must be able to refuse or withdraw consent without being at a disadvantage.
To give consent in an informed manner means:
To know the identity of the organization processing data, the purposes for which the data are being processed, the type of data that will be processed, the possibility to withdraw the given consent, where applicable the fact that the data will be used for solely automated-based decision-making, including profiling if the consent is related to an international transfer and the possible risks of data transfers to third countries.
Performance of a contract - Recital 44
If you are allowed to process data based on a contract, this is always a very good starting point, because you are contractually assured that you are allowed to process data. However, you always must pay attention to what the contract says exactly.
How is your practical process designed, what data do you need, where is the data processed, are third parties involved in data processing, are you allowed to evaluate the data, and if so, in what way?
In any case, the contract represents a secure basis for processing the data.
But you must make sure that the contractual regulations fit your process. If this is not the case, you should conduct a gap analysis to see if you must adjust either the contract or your process.
Fulfillment of a legal obligation to which the controller is subject - Recital 45

If your company has legal obligations that you must comply with, then these can also be the basis for the lawful processing of the data. The legal obligation mustn't mean that you are allowed to process all data of the person concerned without restrictions. As already shown in the case of the contract, you must also compare the legal obligation with the practical process.
Data processing is only lawful in those points where the legal obligation specifically stipulates this.
Vital Interests of the data subject or another natural person - Recital 46
The processing of data from vital interests is legitimate, provided that the data processing is not possible on another basis and vital interests are paramount.
Performance of a task conducted in the public interest or in the exercise of official authority
Tasks conducted in the public interest or the exercise of official authority are always legitimate if the process is consistent with the corresponding task. This always means that the process and the legal requirements must match.
Processing is necessary for the legitimate interests pursued by the controller or by a third party - Recitals 47 and 48
The processing of data based on legitimate interests must always be considered very carefully. This provision can be used to justify most data processing activities. But the legitimate interest can be interpreted very broadly, which can lead to a large number of problems if the interests are not weighed up or the interests weighed up only very superficially.
The controller and the processor should always ask themselves the question of whether they can justify to an external auditor what exactly their legitimate interest was and why their interest outweighs the right to data protection of the data subject.
In this context, the justification is always especially important. In practice, the legitimate interest often leads to problems because those responsible do not deal with the topic at all and simply process the data.
If there is a data protection violation or a data breach and the company is checked by the respective supervisory authority, you must be able to speak and have a reason for all. This applies regardless of whether the data breach occurred in your company or at your data processor. As the person responsible, you not only have to convince yourself of the data security of your processes but also of how your data processor is working for you.
Recital 81 of the GDPR describes the Use of Processors:
To ensure compliance with the requirements of this Regulation in respect of the processing to be carried out by the processor on behalf of the controller, when entrusting a processor with processing activities, the controller should use only processors providing sufficient guarantees, in particular in terms of expert knowledge, reliability, and resources, to implement technical and organizational measures which will meet the requirements of this Regulation, including for the security of processing. The adherence of the processor to an approved code of conduct or an approved certification mechanism may be used as an element to demonstrate compliance with the obligations of the controller. The carrying-out of processing by a processor should be governed by a contract or other legal act under Union or Member State law, binding the processor to the controller, setting out the subject matter and duration of the processing, the nature and purposes of the processing, the type of personal data and categories of data subjects, taking into account the specific tasks and responsibilities of the processor in the context of the processing to be carried out and the risk to the rights and freedoms of the data subject. The controller and processor may choose to use an individual contract or standard contractual clauses which are adopted either directly by the Commission or by a supervisory authority by the consistency mechanism and then adopted by the Commission. After the completion of the processing on behalf of the controller, the processor should, at the choice of the controller, return or delete the personal data, unless there is a requirement to store the personal data under Union or Member State law to which the processor is subject.
If you do not have a reason to process the data, that's always the worst starting point.
As an auditor I can only say at this point, please be able to speak when an audit is being conducted. It is better to have bad or incomplete reasoning than none at all.
You can see from the above statements that there are a large number of regulations that you must observe if you want or have to be GDPR compliant.
OK, let's be serious. What can you do to be GDPR compliant?
What is GDPR compliance and how to achieve GDPR compliance?
In any case, it makes sense to conduct a GDPR audit at regular intervals. The GDPR Audit provides you with insights into where you are already well positioned and where in your company is still a need for development. The GDPR audit should also show a gap analysis where there are specific gaps and what risks result from them. It should offer you the opportunity to manage this data as part of risk management and reduce the risks step by step. It is important to plan for this beforehand as the fines and penalties are simply too high to ignore.
As already shown, you should commission an external auditor to conduct an audit in your company. As a rule, the auditor will conduct the audit using a GDPR compliance checklist. The GDPR compliance checklist enables the auditor to check all relevant areas and thus work at a consistently high level. In addition, you can see which areas in your company are covered by the GDPR compliance checklist and inform the auditor whether there are any unique features in your company. This ensures that no areas are forgotten and that a holistic view of your company will be achieved.

GDPR Compliance Checklist
The GDPR Compliance Checklist is therefore divided into different areas and sub-areas. A typical structure of a GDPR compliance checklist includes the following areas:
Organization and Responsibilities
General Obligations of the Controller
Measures to safeguard the Rights concerned
Ensuring the information obligations towards those affected
Record of Processing Activities and Data Protection Impact Assessment
Setting up contract management for data protection
Handling data breach
Employee Privacy
Hardware, software, and digital systems
Technical and organizational measures
Contract management
Annual Report of the Data Protection Officer
Liability risks
Regarding IT security management, the following points must at least be included in the GDPR compliance checklist:
General aspects such as security management, organization, and data backup concepts.
Infrastructure such as buildings, server rooms, or protection against fire, water, and theft.
Security aspects of IT systems
Network aspects such as VPN, LAN, or WLAN
Applications with points on the security of selected applications such as databases or remote work.
You can find a lot of additional information in Article 25 GDPR and Article 32 GDPR. Suitable Recitals are:
Again, it is important to understand that the GDPR is a data protection law. This is made particularly clear in Recital 75 “Risks to the Rights and Freedoms of Natural Persons”.
The risk to the rights and freedoms of natural persons, of varying likelihood and severity, may result from personal data processing which could lead to physical, material or non-material damage, in particular: where the processing may give rise to discrimination, identity theft or fraud, financial loss, damage to the reputation, loss of confidentiality of personal data protected by professional secrecy, unauthorised reversal of pseudonymisation, or any other significant economic or social disadvantage; where data subjects might be deprived of their rights and freedoms or prevented from exercising control over their personal data; where personal data are processed which reveal racial or ethnic origin, political opinions, religion or philosophical beliefs, trade union membership, and the processing of genetic data, data concerning health or data concerning sex life or criminal convictions and offences or related security measures; where personal aspects are evaluated, in particular analysing or predicting aspects concerning performance at work, economic situation, health, personal preferences or interests, reliability or behaviour, location or movements, in order to create or use personal profiles; where personal data of vulnerable natural persons, in particular of children, are processed; or where processing involves a large amount of personal data and affects a large number of data subjects.
Recital 76 and 77 addresses the need for risk orientation.
The likelihood and severity of the risk to the rights and freedoms of the data subject should be determined by reference to the nature, scope, context, and purposes of the processing. Risk should be evaluated based on an objective assessment, by which it is established whether data processing operations involve a risk or a high risk.
Guidance on the implementation of appropriate measures and the demonstration of compliance by the controller or the processor, especially as regards the identification of the risk related to the processing, their assessment in terms of origin, nature, likelihood, and severity, and the identification of best practices to mitigate the risk, could be provided in particular using approved codes of conduct, approved certifications, guidelines provided by the Board or indications provided by a data protection officer. The Board may also issue guidelines on processing operations that are considered to be unlikely to result in a high risk to the rights and freedoms of natural persons and indicate what measures may be sufficient in such cases to address such risk.
Recital 78 describes approaches for technical and organizational measures.
The protection of the rights and freedoms of natural persons about the processing of personal data requires that appropriate technical and organizational measures be taken to ensure that the requirements of this Regulation are met. To be able to demonstrate compliance with this Regulation, the controller should adopt internal policies and implement measures that meet in particular the principles of data protection by design and data protection by default. Such measures could consist, inter alia, of minimizing the processing of personal data, pseudonymizing personal data as soon as possible, transparency about the functions and processing of personal data, enabling the data subject to monitor the data processing, and enabling the controller to create and improve security features. When developing, designing, selecting, and using applications, services, and products that are based on the processing of personal data or process personal data to fulfill their task, producers of the products, services, and applications should be encouraged to take into account the right to data protection when developing and designing such products, services, and applications and, with due regard to the state of the art, to make sure that controllers and processors can fulfill their data protection obligations. The principles of data protection by design and by default should also be taken into consideration in the context of public tenders.
The GDPR audit needs to consider these aspects to be accurate.
The GDPR audit thus takes a holistic view and evaluates the company from a bird's eye view to find the gaps. This procedure ensures that the controller receives a comprehensive audit report that helps him to initiate the next steps and to minimize the risks.

GDPR compliance can only be achieved through a combination of diverse measures.
GDPR compliance always requires a comprehensive audit to ensure that no essential aspects were overlooked. The audit can be conducted both internally and externally. From my point of view, it makes more sense to conduct an external audit, as this is the only way to ensure an independent evaluation of all measures.
Unfortunately, internal audits always involve the risk that individual aspects are overlooked too quickly or carelessly, or that certain findings simply should not appear in an audit report.
GDPR compliance always requires clear, transparent, comprehensive, and integrity reporting. This is not about assigning blame or showing how good or bad a company is. A GDPR audit is about identifying weaknesses that can be used to minimize risks to achieve GDPR compliance.
However, GDPR compliance also means always being compliant in day-to-day business. This requires that the employees are aware of the regulations of the GDPR and can apply them in everyday life. If the employees are not trained in the GDPR and cannot apply it daily, there will always be errors and problems because the GDPR is just too complex. In addition to training employees, you must also ensure that your processes are GDPR compliant.
Training employees and providing them with valuable information about the GDPR is one thing, making your processes GDPR-compliant is another.
About the training of your employees, you need good training documents (or a digital training tool), you need people in your company who can provide information on questions of your employees and you need a data protection officer (DPO, Art. 38 / Art. 39 GDPR) who continuously accompanies the development of your company and intervenes in a controlling manner.
GDPR Article 25 – Privacy by design and by default
To make your processes GDPR compliant, it already helps a lot to implement the requirements of Article 25.
Privacy by Design
Article 25 of GDPR states the following regarding technology design:
Taking into account the state of the art, the cost of implementation, and the nature, scope, context, and purposes of processing as well as the risks of varying likelihood and severity for rights and freedoms of natural persons posed by the processing, the controller shall, both at the time of the determination of the means for processing and at the time of the processing itself, implement appropriate technical and organizational measures, such as pseudonymization, which are designed to implement data-protection principles, such as data minimization, effectively and to integrate the necessary safeguards into the processing to meet the requirements of this Regulation and protect the rights of data subjects.
Suitable technical and organizational measures are therefore particularly important to achieve GDPR compliance. However, there is no uniform specification here, as the law already states that suitable technical and organizational measures must be taken. Furthermore, the controller has to take into account various aspects of Article 25 GDPR, which are to be considered in a risk-oriented manner. He can therefore not take any cost-effective measures that somehow affect data protection and GDPR compliance. Rather, he must ensure that the technical and organizational measures used are suitable for reducing the risks to an acceptable level.
GDPR compliance is always accompanied by an acceptable residual risk. In the best case, privacy by design leads to GDPR compliance being achieved from the process perspective and thus makes a decisive contribution to reducing risks.
So, Privacy by Design deals with the process-related view of the data that we usually find in software, applications, databases, and so on these days.
Privacy by Default
Privacy by Default stands for reducing the amount of data processed.
Article 25 of GDPR states the following regarding Privacy by Default:
The controller shall implement appropriate technical and organizational measures for ensuring that, by default, only personal data which are necessary for each specific purpose of the processing are processed. That obligation applies to the amount of personal data collected, the extent of their processing, the period of their storage, and their accessibility. In particular, such measures shall ensure that by default personal data are not made accessible without the individual’s intervention to an indefinite number of natural persons.
If a new software or application is delivered, the settings in the product should be set in such a way that they are as data protection-friendly as possible from the user's point of view (privacy by default).
The user should manage his data and should therefore decide for himself which data should be processed and which not. However, applications are often not programmed in this sense, because programmers shall provide the best UX to the customer. This means often that more data is processed than desired by the user. When it comes to privacy by design, we always have to decide between the best possible UX and the most data-friendly setting.
Additionally, Article 25 of GDPR states that:
An approved certification mechanism under Article 42 GDPR may be used as an element to demonstrate compliance with the requirements set out in paragraphs 1 and 2 of this Article.
To be honest, nowadays we want to know exactly how our customers tick and want to create a profile about them. Profiling can be used in many ways but should not play a significant role in this article and is ultimately the opposite of privacy by default.
If you have any questions or would like to contact me, you can reach me at my email address harald@griffox.com.

